Since IPv6 gets more and more important, I am using it by default on all my test firewalls, which of course support IPv6. However, when comparing the different functions and administration capabilities, they vary significantly.
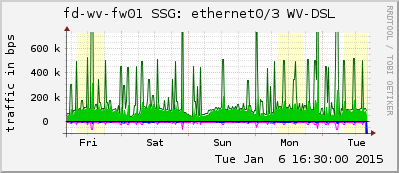
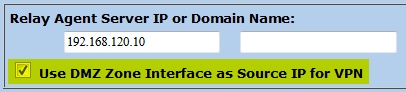
Here comes my short evaluation of the IPv6 functions on the following four firewalls: Cisco ASA, Fortinet FortiGate, Juniper SSG, and Palo Alto.
Continue reading Firewall IPv6 Capabilities: Cisco, Forti, Juniper, Palo