I tested the file blocking features of the Palo Alto Networks next-generation firewall and was a bit confused why several file types still passed the firewall though I set the policy to “any block”. Therefore, I tested a few scenarios with the file blocking security profile and present my test results here.
The tested PAN-OS version was 5.0.9 on a PA-200. I have not used WildFire in these tests.
Benefits
- Allow/block file transfers through various protocols, e.g., http, ftp, smtp, and many more.
- Upload and download are controllable independently.
- True file type detection through a decode of the files and not through a simple comparison of the file extension.
Limitations
- Not a “real” security policy which is passed from top to bottom.
- Certain file types are recognized two or more times as different file types, e.g., “zip and doc” for a single docx document. That is: If an organization wants to allow doc files while blocking zip, this is not possible.
- No whitelist support since “any block” does NOT block anything but only the known file types. (See Palo Alto link at the bottom.)
Own Tests
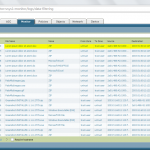
I ran through several test scenarios and present the results in the screenshot below. The test scenarios are written into the file names of all screenshots. So please refer to these file names.
I also uploaded all my test files to http://testfiles.webernetz.net. Anyone is welcome to download these files in order to test his own equipment.
Conclusion
The file blocking feature on the Palo Alto firewall can be used to avoid file up-/downloads that are done accidentally by a trusted user. It cannot be used to block every file type except some explicitly allowed ones such as done with a whitelist. That is: It does not prevent a malicious user from upload certain files to the Internet! It can only slow down the tries to upload files since the malicious user will find an unsupported file type which is led through the Palo Alto without any blocks or log entries.
Links
- Palo Alto: When configuring file blocking, what does the “Any” option actually mean?
- Palo Alto: File Blocking Rulebase and Action Precedence
Featured image “Sperre” by Tabbo107 is licensed under CC BY-SA 2.0.

Hallo,
Verhält sich die Palo mit der aktuellen Firmware noch genau so?
VG
Roger
Hi Roger,
ich habe es zwar nicht getestet, gehe aber stark davon aus. Die Frage ist ja, ob es überhaupt möglich ist, dieses Verhalten zu ändern. Es dürfte nahezu unmöglich sein, ALLE Filetypes dieser Welt zu kategorisieren. Insofern vermute ich, dass das Verhalten generell schon okay ist. Man muss halt nur wissen, wie man damit umgeht.
P.S.: Meine Testfiles sind ja noch online (siehe Link oben). Du kannst es also einfach selber testen, wenn du eine Palo bei dir irgendwo stehen hast. ;)
Awesome, Im getting ready to test this out and you’ve already done all the planning!