I wrote a very small summary of my IPv6 Security master thesis which gives an introduction to several IPv6 security issues. People that are interested in IPv6 security are welcome to read this summary prior to study the whole master thesis. In this way, they will get an overview of IPv6 security issues before they are flooded with too many details. ;) I wrote this article for the RIPE Labs (published here), but since it gives a good overview about my thesis, I publish it here, too.
Introduction
The advent of IPv6 changes not only the network components, but also the security fields. We see new types of attacks or at least variations of the attacks we know from IPv4. This article provides an overview of the IPv6 security vulnerabilities that arise with the launch of IPv6.
1. Attacks against the IPv6 protocol
1.1. Multicast
Via certain multicast messages an attacker can do a reconnaissance attack on a local network. Simply pinging the all-nodes multicast address ff02::1 shows several machines that are alive. Additionally, some Nmap scripts can be used to reveal almost all IPv6 clients on the network via forcing them to generate new (temporary) IPv6 addresses via SLAAC. The corresponding Multicast Listener Discovery messages from the clients, which are sent via multicast, reveal their interface IDs.
1.2. Extension Headers
Inside extension headers an attacker can send information that remain undetected if the intermediary firewalls do not fully check the options of these headers. This kind of attack is called “covert channel”. For example, inside the Hop-by-Hop extension header, the PadN option (which according to the standard must contain zeros), can be filled with any characters. That means, hidden information can be sent via the network layer without touching the upper layer protocols at all.
Another vulnerability arises with the routing header 0 (RH0). With its usage, a Denial-of-Service (DoS) attack between two nodes or firewall bypassing strategies can be performed. But since RFC 5095 deprecated the overall usage of RH0 in 2007, these attacks are not explained here one more time. (Please refer to the RFC for further details.)
2. Attacks against ICMPv6
ICMPv6 plays a key role in the proper usage of IPv6. Especially the Neighbor Discovery Protocol (NDP) messages such as router advertisements (RAs) and neighbor solicitation/advertisements (NS/NA) are needed for the straightforward usage of the new Internet Protocol.
2.1. Router Advertisement Spoofing
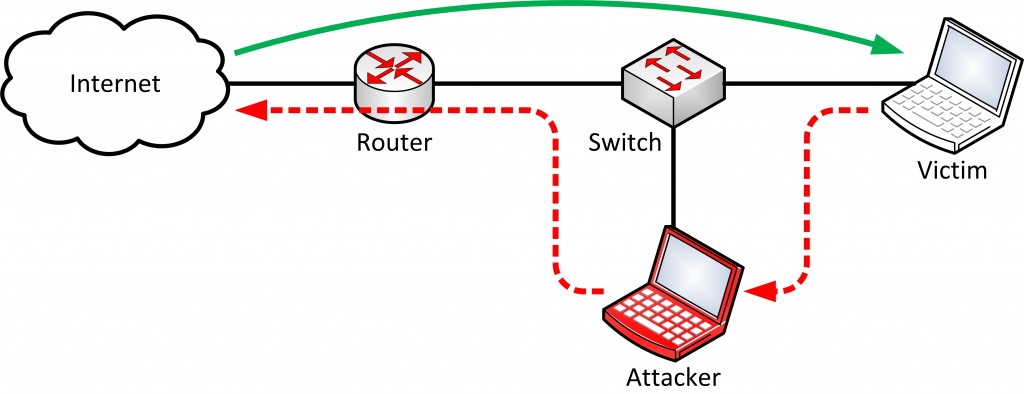
If an attacker sends spoofed router advertisements inside a subnet, all IPv6 nodes will immediately change their routing tables and store the attacker as one of the default routers. If they send traffic to the Internet, this new default router will be used.
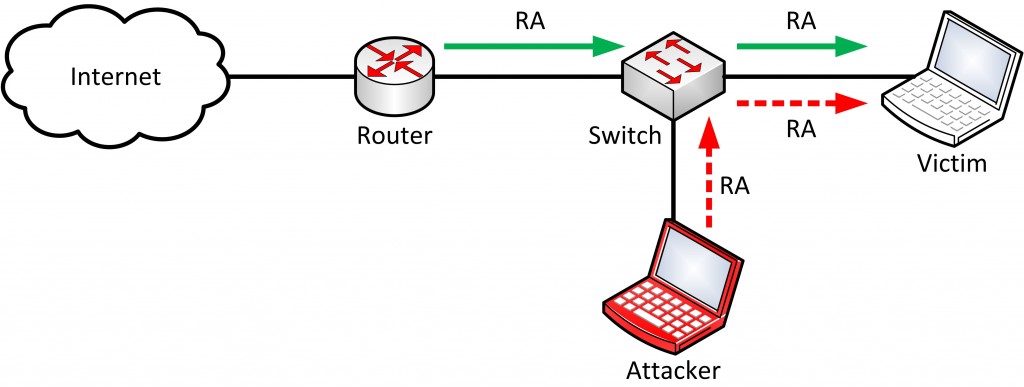
This leads to a situation in which the attacker can fully see (and even modify) all outgoing traffic from the IPv6 nodes to the Internet. This is called a Man-in-the-Middle (MITM) attack. Meanwhile the attacker can not see the returning traffic from the Internet since he is not able to spoof the real default router on the network at this moment. (The attacker can use the neighbor discovery spoofing simultaneously to completely see the traffic.) The following figure illustrates this RA spoofing attack.
2.2. Router Advertisement Flooding
The attacker can also flood many thousand RAs which immediately freezes all Microsoft Windows computers since they are completely overloaded with that many SLAAC processes. This bug is known for many years but still exploitable as of 2015. That means: If an attacker has access to a local network and is not stopped by the intermediary switch while sending spoofed RAs, the complete Windows environment will be frozen!
2.3. Neighbor Discovery Spoofing
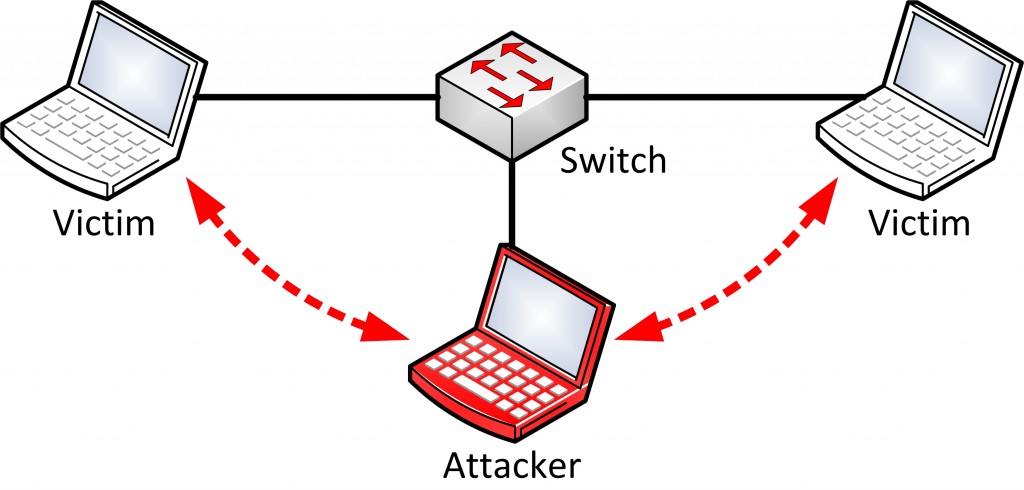
When the attacker spoofs certain neighbor advertisements, he can execute a MITM attack between neighbors. By answering falsified neighbor advertisements to the issued neighbor solicitations from the victims, he redirects all IPv6 traffic over his “routing instance” in the same subnet (see Figure below).
2.4. Duplicate Address Detection
A DoS attack is executed if the attacker answers to all duplicate address detection messages (DADs) from a new IPv6 node with a not yet assigned IPv6 address. The node always believes that this address is already in use and will never get an available IPv6 address and is therefore unable to access the network. This situation remains until the attacker stops the attack.
3. Attacks against DHCPv6
3.1. Address Space Exhaustion
If the concept of stateful DHCPv6 is used, an attacker can exhaust the IPv6 address pool on the server, similar to a DHCPv4 server. Even though the DHCPv6 server could provide enough IPv6 addresses, it has to store a small binding for each address and the corresponding DUID from the client which will at least exhaust the memory of the server if it is flooded with many requests.
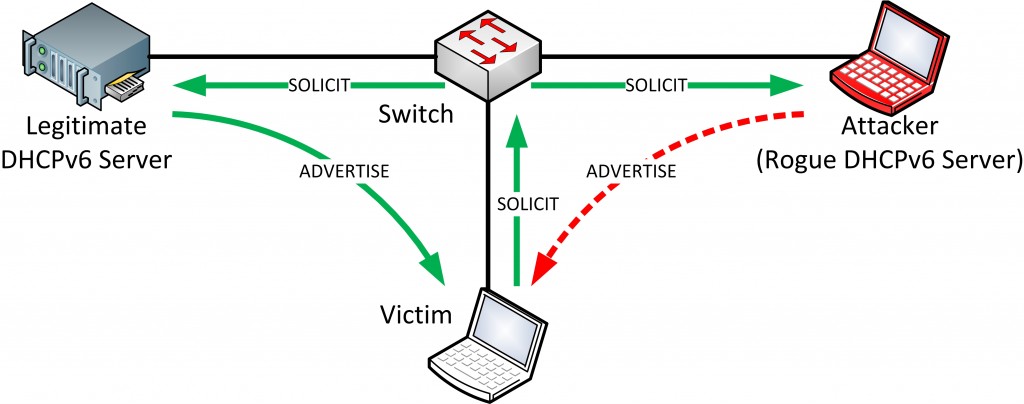
3.2. Rogue DHCPv6 Server
An attacker can also place his own DHCPv6 server inside a network and distribute falsified values, e.g. a spoofed DNSv6 server address. If the clients accept this DNS server, they will get falsified DNS responses from now on if the attacker also owns the spoofed DNS server. With this attack, internal IPv6 users can be redirected to other (web-) servers than they intended to access. The picture below shows the basic attack in the local network.
4. Attack Toolkits
In order to test own equipment and security appliances, the following IPv6 attack toolkits can be used:
- THC-IPv6: The toolkit from Marc Heuse provides many easy to use tools which require almost only the specification of the network interface. Easy.
- SI6 Networks’ IPv6 Toolkit: This package of tools from Fernando Gont can be used in a more precise manner since it can be fine-tuned with many options. Likewise it is more complicated to use compared to the THC-IPv6 toolkit.
- Scapy: To send completely crafted IPv6 packets, the packet manipulation tool Scapy from Philippe Biondi can be used.
5. Conclusion
From a top view, the vulnerability concepts have not changed that much with the advent of IPv6, while the concrete methods are modified to the new protocol. It was possible in IPv4 networks to execute a Man-in-the-Middle attack on the local network as well or to spoof the DHCPv4 server. However, it will still take some time until all network and security devices have a full adoption of all IPv6 defense methods such as RA Guard in switches or explicit extension header detection/filtering in firewalls.
Furthermore, some attacks are possible against the transition methods from IPv4 to IPv6 (not listed here) and of course IPv6 stack implementations in all operating systems will have errors and bugs. That means: Not only the generic IPv6 security issues shown in this summary are relevant for security experts, but also application specific vulnerabilities that are new due to the usage of IPv6.
Featured image “Male Fiddler” by Dave Edens is licensed under CC BY-NC 2.0.



One thought on “IPv6 Security – An Overview”