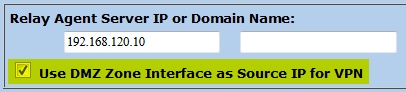
Similar to all my other site-to-site VPN articles, here are the configurations for a VPN tunnel between a Juniper ScreenOS SSG firewall and a Cisco IOS router. Due to the VPN Monitor of the SSG firewall, the tunnel is established directly after the configuration and stays active all the time without the need of “real” traffic.
I am using the policy-based VPN solution on the Cisco router and not the virtual tunnel interface (VTI) approach. That is: No route is needed on the router while the Proxy IDs must be set on the Juniper firewall. (However, I also documented the route-based VPN solution between a ScreenOS firewall and a Cisco router here.)
Continue reading IPsec Site-to-Site VPN Juniper ScreenOS <-> Cisco Router →