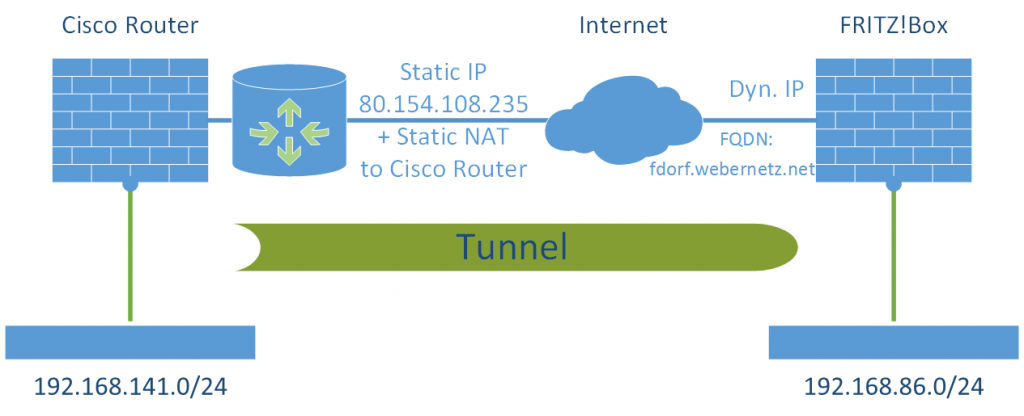
Der Titel sagt eigentlich schon alles: Es geht um das Herstellen eines S2S-Tunnels zwischen einem Cisco Router (statische IPv4) und einer FRITZ!Box (dynamische IP). Ich liste nachfolgend alle Befehle für den IOS Router sowie die Konfigurationsdatei für die FRITZ!Box auf. Für eine etwas detaillierte Beschreibung des VPNs für die FRITZ!Box verweise ich auf diesen Artikel von mir, bei dem ich zwar ein VPN zu einem anderen Produkt hergestellt habe, aber etwas mehr auf die Schritte der Konfiguration eingegangen bin.
Labor
Getestet habe ich die Schose mit einer FRITZ!Box 7270 (FRITZ!OS 05.54) und einem Cisco Router 2621 (12.3(26)). Der Laboraufbau sah dabei folgendermaßen aus:
Cisco Router
Der Cisco Router wird mit nachfolgenden Befehlen konfiguriert. Man achte auf die “crypto dynamic-map dynmap01 …” auf welche in der “crypto map map01 …” referenziert wird. Dem outside Interface wird letztendlich die “crypto map map01” zugewiesen.
Außerdem scheint es mehrere funktionierende Lösungen für dieses VPN zur FRITZ!Box zu geben. Im Internet findet man Konfigurationen, die zum Beispiel beim “crypto isakmp key …” mit “address 0.0.0.0 0.0.0.0” anstatt des von mir vorgeschlagenen “hostname xyz” arbeiten. Auch verwende ich kein “isakmp profile”. Sprich: Meine Methode hier funktioniert, aber es gibt auch andere. ;)
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 |
! crypto isakmp policy 20 encr aes 256 authentication pre-share group 2 lifetime 28800 ! crypto isakmp key Pz5rvYqyU9IzleJSAqnwTTV4yHV95b hostname fdorf.webernetz.net ! crypto ipsec transform-set 3des-sha esp-3des esp-sha-hmac ! crypto dynamic-map dynmap01 1 set transform-set 3des-sha set pfs group2 match address acl-vpn-fdorf ! crypto map map01 3 ipsec-isakmp dynamic dynmap01 ! interface FastEthernet0/0 crypto map map01 ! ip access-list extended acl-vpn-fdorf permit ip 192.168.141.0 0.0.0.255 192.168.86.0 0.0.0.255 ! |
FRITZ!Box
Die anzupassenden FRITZ!Box VPN-Einstellungen sehen so aus:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 |
vpncfg { connections { enabled = yes; conn_type = conntype_lan; name = "fd-wv-ro02"; always_renew = yes; reject_not_encrypted = no; dont_filter_netbios = yes; localip = 0.0.0.0; local_virtualip = 0.0.0.0; remoteip = 80.154.108.235; remote_virtualip = 0.0.0.0; localid { fqdn = "fdorf.webernetz.net"; } remoteid { ipaddr = "80.154.108.235"; } mode = phase1_mode_aggressive; phase1ss = "alt/aes/sha"; keytype = connkeytype_pre_shared; key = "Pz5rvYqyU9IzleJSAqnwTTV4yHV95b"; cert_do_server_auth = no; use_nat_t = no; use_xauth = no; use_cfgmode = no; phase2localid { ipnet { ipaddr = 192.168.86.0; mask = 255.255.255.0; } } phase2remoteid { ipnet { ipaddr = 192.168.141.0; mask = 255.255.255.0; } } phase2ss = "esp-3des-sha/ah-no/comp-no/pfs"; accesslist = "permit ip any 192.168.141.0 255.255.255.0"; } ike_forward_rules = "udp 0.0.0.0:500 0.0.0.0:500", "udp 0.0.0.0:4500 0.0.0.0:4500"; } |
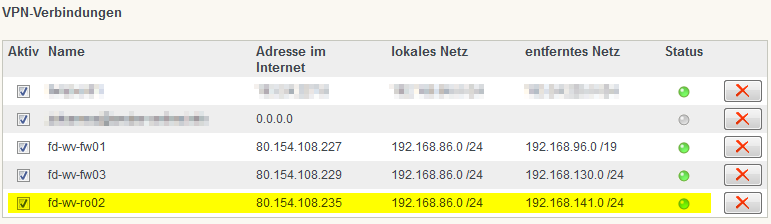
Läuft
Wie man in der FRITZ!Box schön am grünen Bubble erkennen kann:
Beim Cisco Router gibt es die folgenden Befehle, um die Status der einzelnen Security Associations herauszufinden:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 |
fd-wv-ro02#show crypto isakmp sa detail Codes: C - IKE configuration mode, D - Dead Peer Detection K - Keepalives, N - NAT-traversal X - IKE Extended Authentication psk - Preshared key, rsig - RSA signature renc - RSA encryption C-id Local Remote I-VRF Encr Hash Auth DH Lifetime Cap. 518 172.16.1.4 77.1.23.14 aes sha psk 2 00:50:51 ------------------------------------------------------------------------------- fd-wv-ro02#show crypto ipsec sa interface: FastEthernet0/0 Crypto map tag: map01, local addr. 172.16.1.4 protected vrf: local ident (addr/mask/prot/port): (192.168.141.0/255.255.255.0/0/0) remote ident (addr/mask/prot/port): (192.168.86.0/255.255.255.0/0/0) current_peer: 77.1.23.14:500 PERMIT, flags={} #pkts encaps: 4011, #pkts encrypt: 4011, #pkts digest 4011 #pkts decaps: 4021, #pkts decrypt: 4021, #pkts verify 4021 #pkts compressed: 0, #pkts decompressed: 0 #pkts not compressed: 0, #pkts compr. failed: 0 #pkts not decompressed: 0, #pkts decompress failed: 0 #send errors 1, #recv errors 0 local crypto endpt.: 172.16.1.4, remote crypto endpt.: 77.1.23.14 path mtu 1500, ip mtu 1500, ip mtu idb FastEthernet0/0 current outbound spi: C6D78600 inbound esp sas: spi: 0xBAB770F6(3132584182) transform: esp-3des esp-sha-hmac , in use settings ={Tunnel, } slot: 0, conn id: 2090, flow_id: 91, crypto map: map01 sa timing: remaining key lifetime (k/sec): (4602733/3026) IV size: 8 bytes replay detection support: Y inbound ah sas: inbound pcp sas: outbound esp sas: spi: 0xC6D78600(3336013312) transform: esp-3des esp-sha-hmac , in use settings ={Tunnel, } slot: 0, conn id: 2091, flow_id: 92, crypto map: map01 sa timing: remaining key lifetime (k/sec): (4602733/3026) IV size: 8 bytes replay detection support: Y outbound ah sas: outbound pcp sas: ------------------------------------------------------------------------------- fd-wv-ro02#show crypto map Crypto Map "map01" 3 ipsec-isakmp Dynamic map template tag: dynmap01 Crypto Map "map01" 65536 ipsec-isakmp Peer = 77.1.23.14 Extended IP access list access-list permit ip 192.168.141.0 0.0.0.255 192.168.86.0 0.0.0.255 dynamic (created from dynamic map dynmap01/1) Current peer: 77.1.23.14 Security association lifetime: 4608000 kilobytes/3600 seconds PFS (Y/N): Y DH group: group2 Transform sets={ 3des-sha, } Interfaces using crypto map map01: FastEthernet0/0 |
Viel Erfolg! :)


Thank you for this valuable information. This is really good and hope to work perfect.
Can you help me, how this configuration from Fritz! box will change if I have multiple subnets behind the cisco router.
Or in other words
phase2remoteid {
ipnet {
ipaddr = 192.168.141.0;
mask = 255.255.255.0;
}
how can I add one more remote ip network 10.8.0.0/24 in the above configuration?
Hi Shihab,
oh, that’s a good question. I have not tested that yet. Probably this won’t work at all. I asked Google but found nothing.
If your networks are contiguous you can increase the subnet mask, e.g., 10.0.0.0/16. Maybe that helps?
I forwarded your question to AVM via Twitter. Maybe someone of them answers…
Hi all,
we had the same problem (and tried many different things), our solution was:
The required networks have then to be set in the accesslist:
In this config , the Fritzbox routes only the networks in the accesslist over the vpn connection, everything else will be handled normaly.
Hi Patric,
That configuration seems wonderful. Only thing odd is that, my asa has many more site to site tunnels terminated on it. So I will not be in a state to specify 0.0.0.0 0.0.0.0 on phase 2 for this fritz!.
So in my case for example suppose fritz! is serving for 192.168.1.0 And I have
say 172.30.0.0/24 and 10.0.0.0/24 behind the asa
fritz! can have your configuration
But ASA side, I will not be able to specify any any.
So do you think the tunnel will ever form.
My issue is that I dont have a test environment for this one. :-(
Hi Shibab,
the configuration of your phase1 and phase2 has to be the same on ASA and fritzbox.
Why aren’t you able specify 0.0.0.0/0 on your ASA? Is there a network which should not be able to access the fritzbox network or the other way around?
From the view of the ASA “0.0.0.0/0” is the local network, which means all traffic from the fritzbox network will be accepted and all traffic to the fritzbox network will be allowed. The vpn connection will not affect your other networks or connections.
For your issue: make sure the localid-fqdn in your fritzbox config and the connection name in your ASA are the same. The localid-fqdn does not has to be a real fqdn – the ASA does not resolve it. We are using the names of our homeoffice employees (forename.surname) :-)
This works fine if you add a static route on the Fritzbox for that network with next hop gateway ip LAN IP Cisco.
Extend the access list in the FB config for that network:
accesslist = “permit ip any 192.168.141.0 255.255.255.0”,
accesslist = “permit ip any 10.0.0.0 255.255.0.0”;
Be aware of comma and semicolon in the config file !
Also check this url
http://avm.de/service/vpn/praxis-tipps/ueber-vpn-verbindung-zwischen-zwei-fritzboxen-auf-mehrere-ip-netzwerke-hinter-einer-fritzbox-zugreifen/
Patric,
that is the problem. You are specifying any to any in the tunnel specific to fritz! vpn. Now what will happen to the internet traffic for users behind the ASA? What will happen to other vpn network traffic behind ASA. As per the configuration every traffic from behind ASA is an interesting traffic towards the fritz! tunnel, correct?
Well, I think you noticed it already, but for the rest of the readers:
It’s not a any to any tunnel. It’s a any to fritzbox network tunnel.
Thanks Patric,
I took a chance and that worked. Thanks a lot for the idea and thank you Weber for this blog.
Hey, ich habe einige Zeit nach einer guten Anleitung für eine CISCO – Fritzbox VPN gesucht. Danke!
Unter Umständen müssen noch NAT Regeln erstellt werden.
Hi,
Is’s look like a good article.
I need one side permanent VPN connection from Fritz!box to company’s network so It is working only with the one subnetwork which i’m writing in required field. So will this work if I will write 0.0.0.0/0 in “IP network of the company’s VPN:” field and then add access list in Fritz configuration file?
Hey Nick. As far as I know, this won’t work, unfortunately. :(
Hey Johannes. Thank you for you answer. Maybe you have any idea how to solve that problem. In the cisco router the IP routing is configured so for example the VPN configured in my iPhone is working correctly. But as I understood Fritz!Box accessing only to subnetwork which is written in “IP network of the company’s VPN:” field.
Hey Nick. Of course, you can just test it. (Maybe only if you have physical access to the Fritzbox in case it is not working anymore…)
If it’s not working and you still have to implement that scenario, you have to look for a more enterprise-like router. While the Fritzbox is a profound device, it’s still only a home router, not an enterprise router, unfortunately.